Quantum-Safe Networking: Preparing Your Infrastructure for Tomorrow’s Security Threats
- 22 April 2026

Quantum computing represents one of the most significant challenges facing network security today. Unlike classical computers, quantum computers leverage quantum mechanics to solve complex mathematical problems exponentially faster, posing a serious threat to the encryption standards that protect sensitive data across government, finance, healthcare, and defence sectors.
Yet despite the urgency, most organisations remain underprepared. According to ISACA’s 2025 report, 62% of technology professionals are concerned that quantum computing will break current encryption, yet only 5% have made it a high-priority issue. The same report found that just 5% of organisations have a defined quantum computing strategy or roadmap in place.
The window to act is now. NIST has already declared that widely used encryption standards will be deprecated by 2030 and fully disallowed by 2035. For IT leaders and CISOs, this is not a future problem. It is a present one.
Classical Computing vs. Quantum Computing: What’s the Difference?
To understand why quantum computing poses such a significant threat, it helps to understand how it differs from the technology we rely on today.
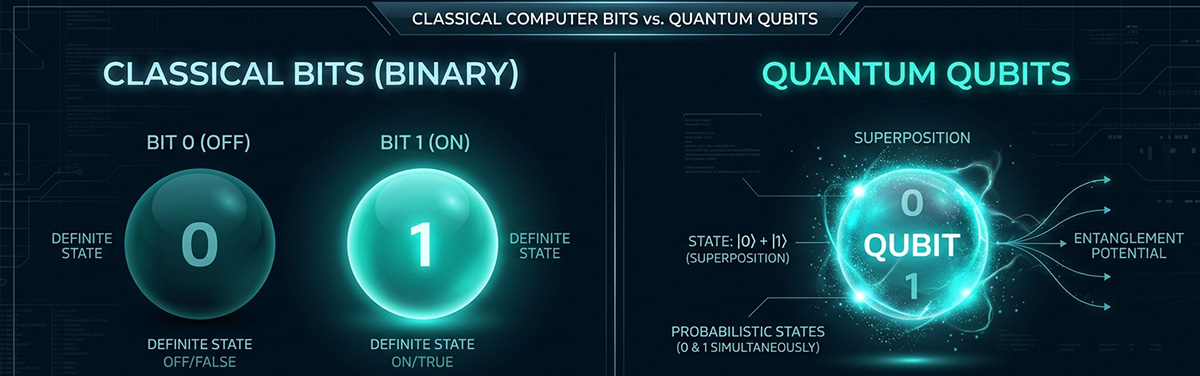
Classical computers process information using bits, values of either 0 or 1. Every operation is sequential, and security protocols like RSA encryption are built on mathematical problems that classical computers would take thousands of years to solve. This is the foundation of modern network security.
Quantum computers operate differently. They use quantum bits, or qubits, which can exist in a state of superposition, effectively representing 0 and 1 simultaneously. This allows quantum computers to process multiple possibilities at once, enabling them to solve certain mathematical problems exponentially faster than any classical machine.
One such algorithm, known as Shor’s algorithm, can factor large numbers at a speed that renders RSA encryption vulnerable. The same applies to Elliptic Curve Cryptography (ECC), which underpins digital signatures and key exchange protocols used across the Internet today.
It is worth distinguishing between quantum computing and quantum Internet. Quantum Internet, which would use quantum properties such as entanglement and superposition to enable theoretically unhackable communication, remains decades away with large-scale infrastructure not expected before 2040 or beyond. However, the quantum computing threat to today’s encryption is expected to arrive far sooner. This gap is precisely what makes the current moment so critical for IT and security teams.
The Immediate Threat: How Quantum Computing Will Impact Network Security

Vulnerabilities in Current Encryption
Most of the encryption standards protecting enterprise networks today were designed with classical computing in mind. RSA encryption relies on the extreme difficulty of factoring large numbers, a task that quantum computers using Shor’s algorithm can perform exponentially faster. ECC faces the same vulnerability through a similar mathematical weakness.
Symmetric encryption such as AES-256 is more resistant to quantum attacks, though its effective security level is reduced. For now, it remains adequate, but it is not immune.
For organisations relying on RSA or ECC to protect sensitive communications, data at rest, or network traffic, the implications are significant. These are not obscure or legacy protocols. They are the backbone of most enterprise security infrastructure today.
The “Harvest Now, Decrypt Later” Threat
Perhaps the most pressing concern is not what quantum computers will do in the future. It is what adversaries are doing right now in preparation.
Advanced Persistent Threats (APTs) are already executing what security researchers call “harvest now, decrypt later” campaigns. These threat actors collect encrypted data today, store it, and plan to decrypt it once quantum computing capabilities mature. As Sectigo notes, financial institutions that retain sensitive records for 7 to 10 years due to regulatory requirements face particularly prolonged exposure.
This means the threat is not hypothetical. Data being transmitted and stored today could be compromised within the decade, well within the operational lifetime of most enterprise systems and the sensitivity windows of most regulated data.
Sectors Most at Risk
While all organisations that handle sensitive data should be concerned, certain sectors face heightened exposure:
- Finance and banking: Long data retention periods create extended windows of vulnerability to future decryption attacks.
- Government and defence: Classified communications and strategic intelligence are high-value targets for state-sponsored threat actors.
- Healthcare: Patient records and medical histories carry long-term sensitivity and are subject to strict data protection obligations.
- Telecommunications: Network infrastructure that underpins national critical services is a prime target for disruption.
Singapore’s Quantum Technology Initiatives

Singapore is taking the quantum threat seriously at a national level, making it one of the most proactive countries in the region when it comes to quantum-safe infrastructure.
The government invested S$121.6 million in the Quantum Engineering Programme (QEP), comprising S$25 million in Phase 1 (2018 to 2023) and S$96.6 million in Phase 2 (2020 to 2025), to build research capability and accelerate quantum technology development (National Quantum Office Singapore). In May 2024, Singapore’s Deputy Prime Minister announced a further commitment of nearly S$300 million into the National Quantum Strategy over the next five years, reinforcing Singapore’s ambition to become a leading quantum technology hub (PR Newswire).
On the infrastructure side, the National Quantum-Safe Network (NQSN) initiative is actively working to design and maintain a quantum-safe communication platform protected by the laws of quantum physics. Phase 1 (2022 to 2025) received S$8.5 million in funding and is hosted by NUS (Fraunhofer Singapore). Coordinating all of this is the National Quantum Office (NQO), established in 2022 to oversee quantum Research, Innovation, and Enterprise activity across the country.
For businesses operating in Singapore, these initiatives signal a clear regulatory and policy direction. Quantum-safe readiness is not just a technical consideration. It is becoming part of the national security and digital infrastructure agenda.
Why Businesses Need to Act Now
The case for early action is straightforward: the longer an organisation waits, the greater its exposure, and the harder the transition becomes.
Nearly two in five organisations globally plan to initiate their post-quantum cryptography transition within the next two years, according to ISACA’s 2025 report. Those that move first will have time to test, validate, and embed new solutions without the pressure of regulatory deadlines or active quantum threats.
Organisations that delay risk two compounding consequences: being caught with vulnerable infrastructure when quantum computers reach sufficient capability, and falling behind compliance timelines as regulators enforce quantum-safe standards. With NIST’s 2030 deprecation deadline approaching faster than many expect, the transition needs to begin well in advance, not at the deadline itself.
Quantum Key Distribution (QKD) and Post Quantum Cryptography (PQC): Solutions Available Today

Quantum Key Distribution (QKD): For organisations that require the highest levels of confidentiality, Quantum Key Distribution (QKD) offers a different approach. Rather than relying on mathematical complexity, QKD uses the fundamental properties of quantum mechanics to establish encryption keys. Any attempt to intercept the key exchange is physically detectable, offering theoretical immunity to cryptanalysis, including attacks from future quantum computers.
QKD is particularly well suited for government agencies, financial institutions, and operators of critical infrastructure where absolute confidentiality is non-negotiable. The QKD market reflects this growing demand, projected to reach USD 2.58 billion by 2030 at a CAGR of 33.78% (Mordor Intelligence).
Post-Quantum Cryptography (PQC): This is a new generation of encryption designed to remain secure even against the threat of future quantum computers. Unlike traditional methods such as RSA and ECC, which could eventually be broken by quantum technology, PQC uses advanced mathematical approaches that are resistant to both classical and quantum attacks.
SPTel’s Quantum-Safe Networking Solutions

For organisations in Singapore looking to future-proof their network security, SPTel offers solutions designed to address the quantum threat at both the infrastructure and application layer.
SPTel’s Quantum Key Distribution (QKD) solution provides quantum-safe protection for critical infrastructure and sensitive data transmission. Built on unique fibre pathways that run alongside power network cables, SPTel’s network is engineered to support quantum-safe networking without requiring disruptive infrastructure overhauls, a meaningful advantage for organisations planning a phased transition.
SPTel’s software-defined network also allows security protocols to be deployed and updated across the network remotely and on demand. This flexibility is essential for crypto-agility, enabling organisations to adopt new post-quantum cryptography standards as they evolve without operational disruption.
To support PQC deployments, SPTel has partnered Fortinet for customer premise equipment (CPE) that can deliver a practical, managed pathway towards post-quantum cryptographic resilience for enterprise customers. Fortinet’s PQC enabled CPEs that serve as the secure customer edge when placed at branch offices, campuses, data centres or remote sites. This supports for policy enforcement, segmentation, encrypted connectivity and threat protection without requiring a full redesign of the underlying WAN from the outset. Integrated with SPTel’s connectivity, the solution acts as a layered service with SPTel providing the resilient underlay through local, international and data centre connectivity, while the PQC enabled CPE secures the edge and protects traffic entering or leaving the customer environment.
From a customer perspective, combining QKD and PQC solutions in a hybrid approach to quantum security results in stronger security, better operational clarity and improved cost efficiency. Instead of treating connectivity, encryption and cyber defence as separate workstreams, the SPTel and Fortinet combination can be presented as one coordinated solution that brings together resilience, manageability and future-readiness.
For workloads requiring low-latency quantum-safe operations, SPTel’s Edge Cloud infrastructure, housed within Critical Information Infrastructure (CII) nodes, supports quantum-safe cryptographic operations at the network edge with sub-millisecond latency.
With SPTel, you can build a network that is not just secure today, but ready for the security demands of tomorrow.
Key Milestones: The Quantum-Safe Timeline
Understanding the timeline helps IT and security leaders prioritise action and plan transitions effectively.
| Year | Milestone |
| 2025 to 2030 | Critical transition window. Organisations should complete post-quantum cryptography migration before quantum threats materialise |
| 2030 | NIST deadline: RSA-2048 and ECC-256 officially deprecated |
| 2035 | NIST deadline: RSA-2048 and ECC-256 fully disallowed |
| 2030 to 2040+ | Full quantum Internet deployment remains uncertain; infrastructure development continues |
Table 1: Critical milestones as outlined by NIST
The key insight here is that quantum-safe networking is not about waiting for quantum Internet. It is about protecting current networks and data from quantum computing threats that are expected to arrive within the next decade. The deprecation deadlines are not the starting line. They are the finishing line. Preparation needs to start now.
Secure Your Infrastructure Before It Is Too Late

The quantum threat is not on the horizon — it is already shaping how adversaries operate today. With Singapore’s S$300 million national quantum strategy and NIST’s 2030 deprecation deadline approaching, the direction is clear. For IT leaders and CISOs, early action means staying ahead of both the threat and the regulatory curve.
Quantum Key Distribution is commercially available and deployable today. There is no reason to wait.
With SPTel, you can implement quantum-safe cryptography and secure your critical infrastructure before the window closes. Explore SPTel’s Quantum Key Distribution and quantum-ready network solutions today.











